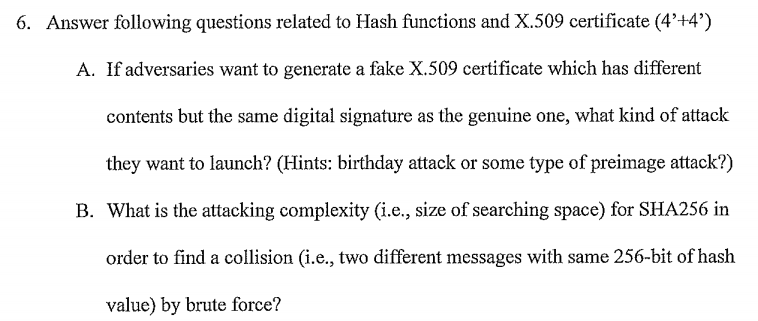
6. Answer following questions related to Hash functions and X.509 certificate (4’+4′) A. If adversaries want to generate a fake X.509 certificate which has different contents but the same digital signature as the genuine one, what kind of attack they want to launch? (Hints: birthday attack or some type of preimage attack?) What is the attacking complexity (i.e., size of searching space) for SHA256 in order to find a collision (i.e., two different messages with same 256-bit of
PayPal Gateway not configured
PayPal Gateway not configured